Cyren Resources Center
On-demand Webinars
Security Practices
The Hidden Costs Beyond The Inbox
Recorded June 01, 2022
Watch this podcast-style event where Michael Sampson and Mike Fleck comment on the cardinal points in the recent 2022 Osterman Research report.
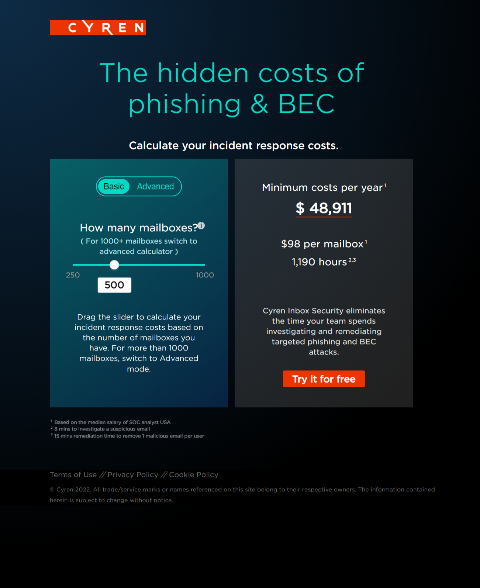
The Hidden Costs of Phishing & BEC
Recorded April 05, 2022
Attend this podcast-style event to learn how Fluid Networks dramatically reduced the time their analysts spend managing the problem of phishing, BEC, and user education.
Better Together! Cyren + KnowBe4 Provide A Comprehensive Solution To Phishing and BEC
Recorded March 08, 2022
Attend this joint webinar by Cyren and KnowBe4 to learn how their integrated solution ensures organizations get the most value from user training, advanced threat detection, and automated incident response to improve defense against phishing and BEC threats.
Use Security Maturity to Gain Strategic Ground Against Phishing
Recorded April 05, 2022
CISO have to switch from board-level communication to detailed technical architectures and monitoring of organization-wide processes. The ability to show value and gaps to the board yields the CISO’s budget, while command of organizational details ensures the necessary controls are in place and properly maintained to keep risks at acceptable levels. …
Starting the Path to Zero Trust in Microsoft Cloud
Recorded December 01, 2021
The company network perimeter no longer exists as the security boundary business. With the large adoption of hybrid work and the expectation that even after the COVID-19 pandemic is under control, businesses will not go back to a full in-office work model. In a hybrid work model, the Internet has become the network perimeter.
The roles of users and machines in the fight against phishing
Recorded July 28, 2021
Protecting your organization from phishing, BEC, and ransomware requires four effective pillars: prevention, detection, incident response, and prediction. During this webinar, we will discuss the different technologies required and how to leverage user education to stop phishing attacks, increase user productivity, and avoid alert fatigue.
How to stop Phishing Threats for Office 365
Recorded July 07, 2021
Digital Pathways have been in the Cyber Security market for nearly 25 years and seen a continuous rise in data security breaches. Our suite of products and services enables our clients to monitor their security posture, balance business risk with cyber risk, and achieve a cost-effective way to keep their data safe. …
Alerts Don’t Remediate Themselves: Best Practices for Dealing with Cyber Threats
Recorded April 28, 2021
Evasive phishing, BEC, and fraud attacks are getting past existing email defenses. The sophistication of these attacks helps them avoid perimeter detection and fool your employees, including those who’ve been through Security Awareness and Training programs.
Significantly reduce security incidents arising from phishing attacks
Recorded May 26, 2021
With over 91% of Cyberattacks starting with a phishing attack, getting your email defences right has never been more important. But why is it, when almost everyone has email security, does this statistic remain largely constant year after year? …
How to remediate Office 365 Phishing Failures
Recorded March 10, 2021
Organizations using Microsoft 365’s email platform consistently report higher rates of successful evasive phishing attacks. And it’s no surprise — even Microsoft’s native Advanced Threat Protection (ATP) and Exchange Online Protection (EOP) have malicious catch rates of 0.15 percent, which is significantly lower than the rate of other solution providers. …
Understanding Threats
A New Paradigm For Malware Analysis
Recorded September 21, 2022
Watch this on demand webinar to learn about Cyren’s new product (Hybrid Analyzer), which allows service providers, technology companies, and large enterprises to inspect files at speed, at scale, and without breaking the bank (i.e, NOT a sandbox).
How to stop Phishing Threats for Office 365
Recorded November 17, 2021
Watch this on demand panel discussion to address why and how to stop phishing messages making it past traditional Secure Email Gateways and reaching users’ inboxes.
Analysis of phishing kits
Recorded October 06, 2021
A phishing kit includes the web pages and software code used to display mirror images of legitimate services and collect exposed credentials, payment information, and other sensitive data. This webinar is a behind the scenes look at phishing kits.
Quarantined and Exposed: Evolving Threats in a Remote Working World
Recorded May 28, 2020
Attackers have consistently leveraged current world events to their advantage by evolving their attack TTPs to bypass perimeter defenses. Overnight, COVID-19 has caused enterprises to deploy technologies, policies, and resources to enable employees to work remotely. …
Phishing Threats Overview for Legacy Gateways and Microsoft 365
Recorded April 02, 2020
Cyren’s latest threat report discusses how phishing attacks continue to circumvent legacy security gateways and are the top threat targeting businesses. From massive-scale, botnet-driven outbreaks to highly focused attacks using business email compromise (BEC), spear phishing, and whaling techniques – every company and employee is at risk of becoming a target.
Malware in 2020: Recent Trends and What Is Coming Next
Recorded February 27, 2020
Malware authors continue to evolve distribution and coding techniques to get their software past your security. In this webinar, Arna Magûsardóttir, Cyren’s lead analyst for Global Threat Detection, will explain key malware trends from 2019 and provide analysis of representative malware techniques, as well as an outline what we might expect to see from malware developers (and what security teams should prepare for) during 2020.
How Evasive Phishing Is Fooling Your Security
Recorded July 25, 2019
Join Cyren threat researcher Tinna Sigurdardottir and industry security product veteran Duncan Mills to learn the top categories of evasive phishing techniques being applied by phishing campaign developers today, and why the use of such techniques is on the upswing.
“Fileless” Ransomware: The Next Big Thing?
Recorded September 20, 2018
Mass ransomware attacks have receded in volume this year, but the rising use of super stealthy “fileless” ransomware, where no malicious executable is ever saved to disk, poses challenges for detection and complicates mitigation.
How Evasive Malware-as-a-Service is Changing Internet Security
Recorded May 24, 2018
Malware authors continue to evolve distribution and coding techniques to get their software past business security. In this webinar, Senior Solutions Engineer Tom McNash will review the rise of the malware service industry on the dark web, which is facilitating new malware attacks and contributing to rising volumes of more sophisticated malware.
Company And Product Information
Threat Engines
Inbox Security
Threat InDepth
Reports And White Papers
Cyberthreat Reports
White papers