

DRPS stretch detection and monitoring activities outside of the enterprise perimeter by searching for threats to enterprise digital resources, such as IP addresses, domains and brand-related assets. DRPS solutions provide visibility into the open (surface) web, dark web and deep web environments by providing contextual information on threat actors and the tactics and processes that they exploit to conduct malicious activities.
Why Threat InDepth?
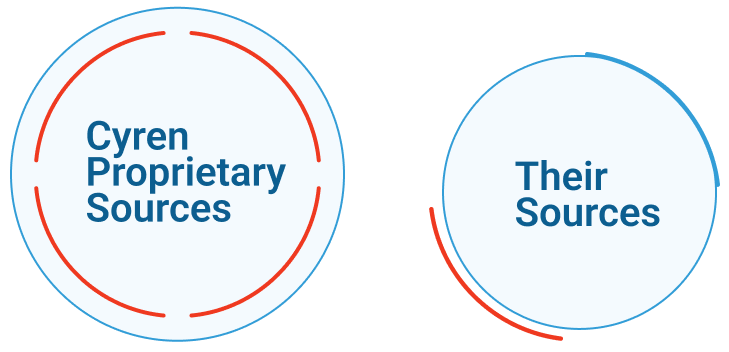
Most threat intelligence vendors purchase data from similar sources before repackaging and selling it. Valuable information gets buried within mountains of old information and false positives.
Malware File and URL Intelligence
Real-time information about ongoing and emerging malware threats Analyze millions of suspicious files to detect hundreds of thousands of new malicious files daily Contextual information includes malware family and relationships to IP addresses, download URLs, and other IOCs
Phishing and Fraud URL Intelligence
Visibility of over 1 Billion URLs each day. Analyze URLs strings and web content to detect zero day and other phishing attacks. Over 9,000 new phishing URLs per day Context includes brand and industry information and is correlated to IP addresses that host the pages and files that contain phishing links
IP Intelligence
Analyze billions of web and email transactions in real-time to expose high-risk IP addresses that serve spam, phishing, and malware Apply unique technologies and algorithms to quickly identify botnets and zombie hosts, and their activity Contextual information includes threat intensity, risk score, geolocation, and relationships to other threats

A buyer’s guide to actionable email threat intelligence
By providing security analysts with actionable threat intelligence, organizations can better understand –
and prevent – threats.
Security teams play a constant cat-and-mouse game with rapidly evolving phishing attacks.Cyren’s Threat Intelligence Feeds provide unique, high-fidelity, actionable threat intelligence before other vendors.
Threat Intelligence
Threat InDepth
Spot cyber attacks before they hit with real-time technical threat intelligence feeds of emerging malware and phishing threats.Elevate Your Strategy!
Download the Complete Competitive Analysis for IP Reputation Now.
Unlock valuable insights into the strengths, weaknesses, and strategic differentiators of Data443's Cyren Threat Intelligence and the IP Reputation Engine
You Might Also Find This Interesting
Data Identification Manager™
Malware, spyware, rootkits, bots, trojans, and any other types of internet security threats
Access Control Manager™
Passwordless Access Control for
the Enterprise
Data Classification
Scan a file for classification of 1300+ global sensitive data policies in 40+ languages within seconds
Data Hound™
Free Live Data Classification for Sample Reporting