There appear to be only two things that are certain in life: death and cybercriminals trying to steal your tax refund.
As governments have moved tax systems online to facilitate life for the taxpayer, refund scams using phishing and social engineering to obtain personal financial information have become epidemic, with criminals diverting any tax refund due or even gaining access to personal bank accounts to steal funds directly.
The Malaysian Tax Fraud Phish — 17 Banks!
This week’s case study is from Malaysia, which has drawn particular attention due to the elaborate set of fraudulent banking pages created for the scam — in addition to the fake government refund “landing page” linked from the phishing email, there are fake login pages for no less than 17 (!) Malaysian banks linked to the landing page.
This week the Malaysian government went so far as to issue an official warning, alerting taxpayers to watch out for fraudulent emails containing information about overdue tax refunds. This phishing campaign appears to be leveraging the Malaysian Inland Revenue Board’s move to facilitate tax payments through an online payment gateway known as Financial Process Exchange (FPX).
Cyren detects and blocks the following domain and IP addresses associated with the phishing threat: lucyhanselman[.]nl and IP Address : 95.211.13.70. A list of fraudulent phishing URLs detected and blocked by Cyren are provided at the end of the article.
How It Works
The scam arrives via email with an attached document containing instructions on how to claim an overdue tax refund. The phishing document is distributed using the Office Open XML document format (.DOCX), with the malicious link to the phishing site landing page obfuscated as a shortened URL. (We recently highlighted this URL-shortening obfuscation technique in the blog article: Bank Phishing Scam Using Shortened Links.)
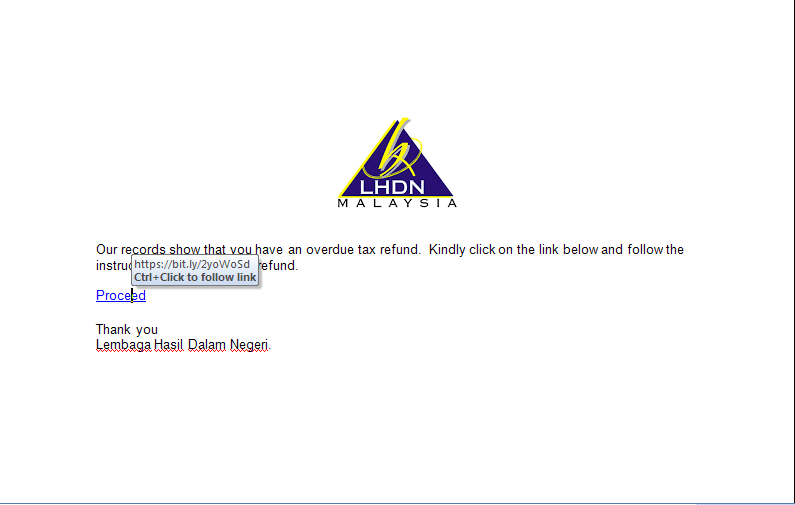
Phishing document sent to Malaysian citizens containing a shortened URL used to obfuscate a malicious hyperlink.
Once a user clicks on the shortened URL, he is redirected to a web page displaying a list of banks similar to the actual affiliate banks displayed on the real Malaysian Inland Revenue Board’s web site. The fake landing page instructs the victim to choose his own bank from a list of 17.

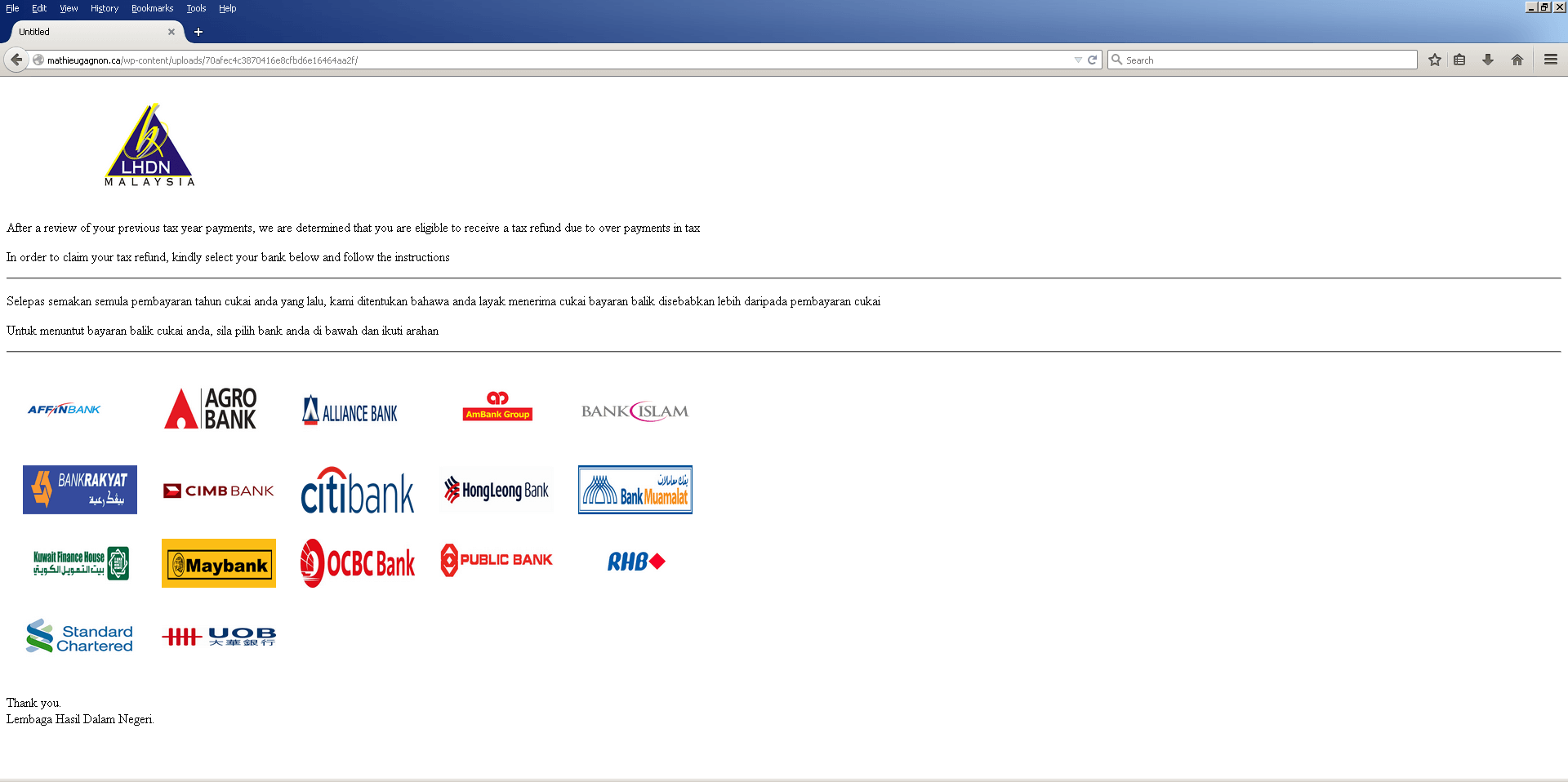
Top: The list of FPX affiliate banks from the actual Malaysian government site (https://byrhasil.hasil.gov.my)
Bottom: The phishing scam’s website with a list of 17 banks that are the same as the real government site.
When the victim clicks on the fake bank logo, he is taken to a phishing page. As you can see from the examples below, the fake bank pages look highly legitimate, although a quick scan of the webpage names clearly shows an incorrect URL.
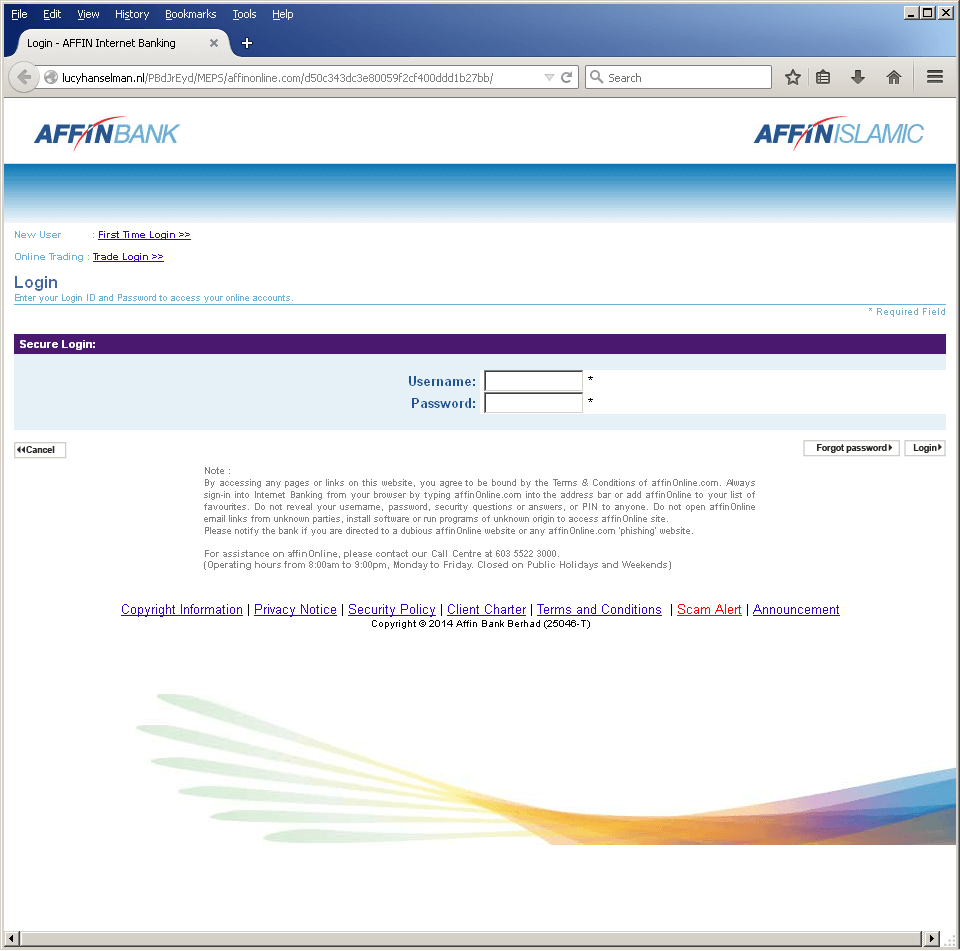
Phishing page for AFFiNBank
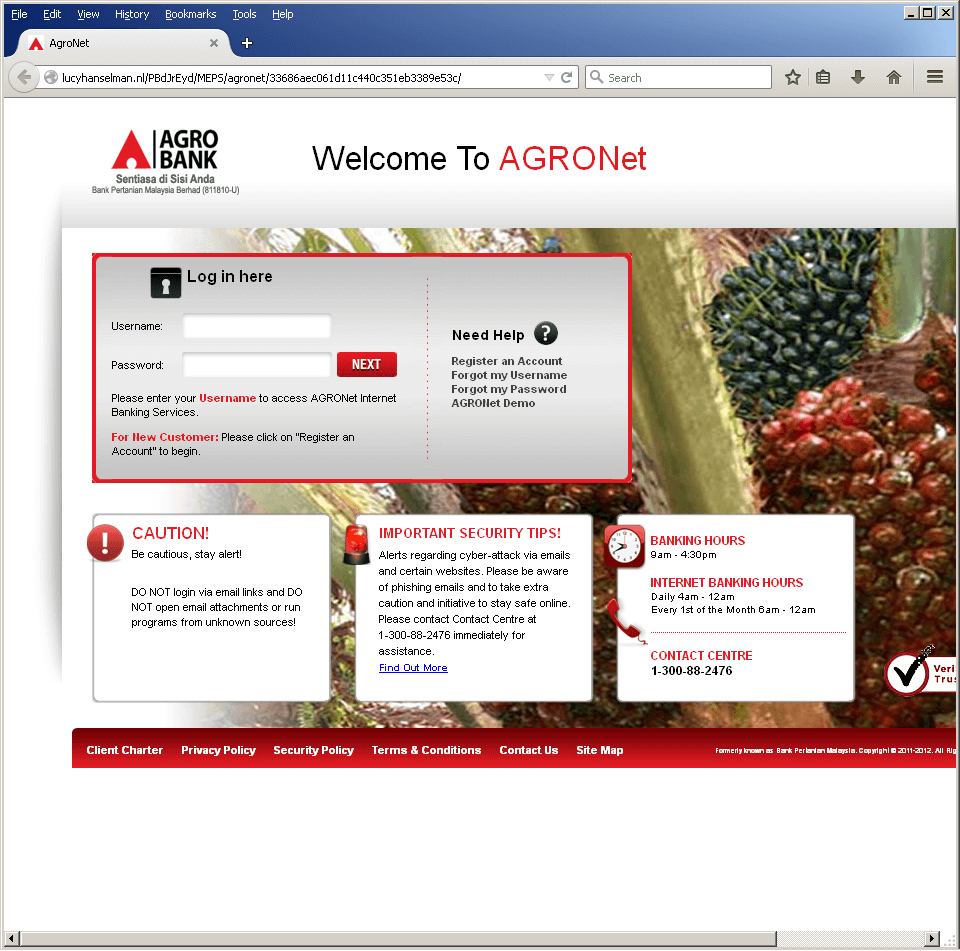
Phishing Page for Argo Bank
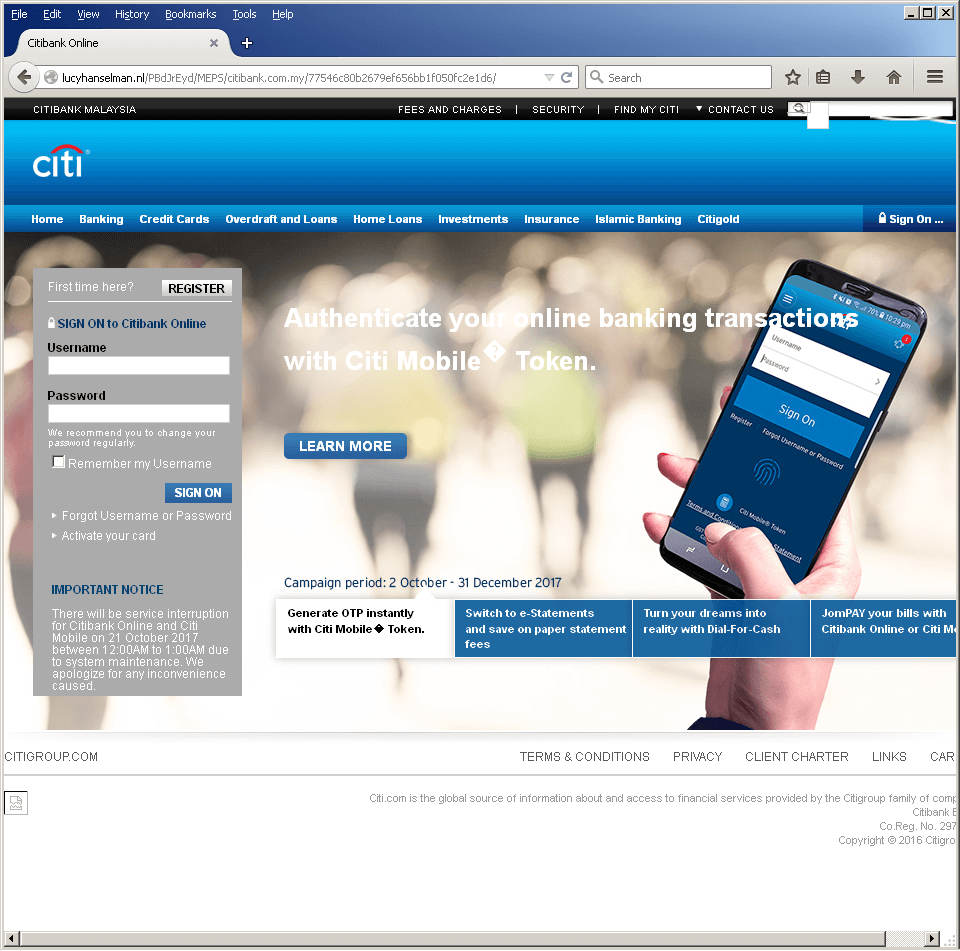
A very real looking (but fake) Citibank login page.
After accepting the victim’s login credentials, the criminal then attempts to collect more personal and sensitive information by redirecting the victim to a few more verification pages, each time asking the victim to enter a one time password/PIN (OTP) to make the scam appear legitimate and convincing.
Additional user information requested by this campaign includes:
- E-mail address
- Phone number
- Last 4-digits of account ID
- Mother’s Maiden Name
After entering details, the phishing site then goes into a loop, requesting the victim’s Mother’s maiden name over and over again.
Think Before You Click! Prevent Financial Phishing
With individuals and companies around the globe becoming targets (and often victims) of tax refund and banking phishing scams, it is critical to implement strong email gateway security which can prevent phishing emails from reaching users in the first place. Email gateway security also blocks access to phishing links as a second layer of protection.
In addition, Cyren encourages anyone to “think before you click.” If you suspect fraud, type the address of your financial institution directly into your web browser.
Other ways to test the reliability of a financial site include:
- Look at the URL to see if it displays the financial organization’s name, along with the “lock” icon to indicate you are using a secure connection.
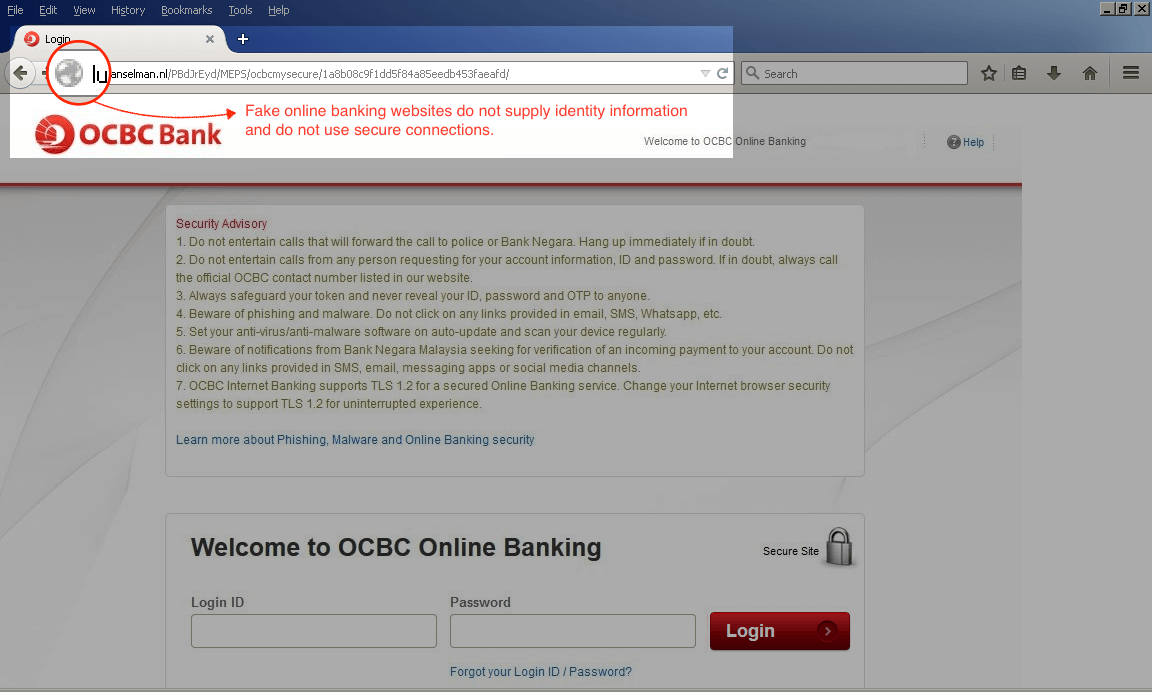
A fake online banking login page will not supply a security login icon or a correct URL address.
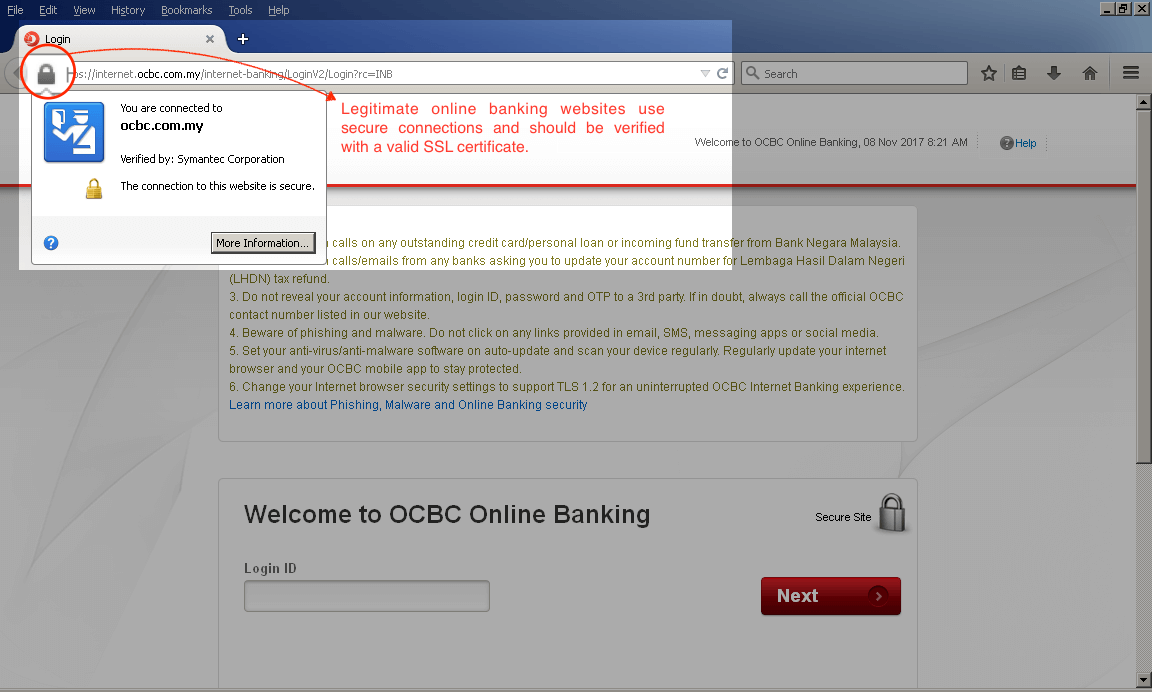
Signed and verified online banking login page.
- Enter fake credentials. It may sound counter-intuitive to do this, but a fake online banking website will typically just accept any login credentials and then redirect the user to more phishing pages to collect other types of sensitive information. Legitimate banking sites will automatically recognize the fake credentials and display a message that says the user name and password are incorrect or cannot be found.
Indicators of Compromise and Cyren Detection
Cyren detects and blocks the following URLs associated with this threat:
| Hash/URL | Object Type/Phishing Target | Remarks |
| 287ec5f40eeab28918ce7063ecb724a7f19f4f7647ff17906e105e85dc55688e | Office Open XML Word Document | Detected by Cyren as XML/Phish.J |
| hxxp://www[.]jornalodiasp[.]com[.]br/wp-admin/images/index[.]php | Phishing URL | Blocked by OpenDNS |
| 119cdd88a034ad906bfc154cc7280adae7b798419e84be7b24bd3fdca6a1228d | Office Open XML Word Document | Detected by Cyren as XML/Phish.K |
| hxxps://bit[.]ly/2yoWoSd | Shortened Phishing URL | |
| hxxp://mathieugagnon[.]ca/wp-content/uploads/70afec4c3870416e8cfbd6e16464aa2f/ | Phishing URL | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/affinonline.com/* | AFFin Bank | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/agronet/i* | Agro Bank | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/allianceonline.com.my/* | Alliance Bank | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/ambank/* | AmBank Group | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/bislam/* | Bank Islam | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/irakyat.com.my/* | Bank Rakyat | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/cimb/* | CIMB Bank | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/citibank.com.my/* | Citi Bank | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/hlbconnect/* | HongLeong Bank | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/i-muamalat.com.my/* | Bank Muamalat | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/kfh.com.my/* | Kuwait Finance House | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/mbb/* | MayBank | |
| hxxp://lucyhanselman[.]nl/PBdJrEyd/MEPS/ocbcmysecure/* | OCBC Bank | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/pbeonline/* | Public Bank | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/rhb.com.my/* | RHB | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/scb/* | Standard Chartered | |
| hxxp://lucyhanselman[.]nl//PBdJrEyd/MEPS/uob/* | UOB |