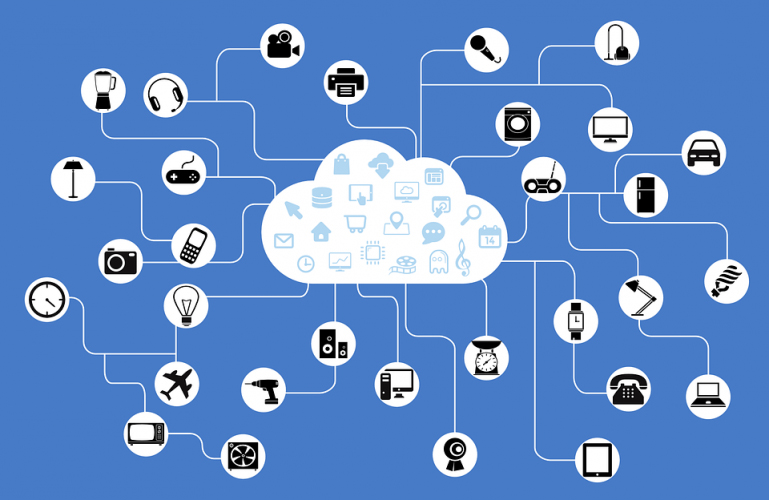
 For several years, cybersecurity professionals have been predicting an impending malware onslaught originating from Internet of Things (IoT) devices—“smart” everyday household items that can connect to the Internet, such as refrigerators, WiFi routers, DVRs, baby monitors, security cameras, thermostats, and so forth.
For several years, cybersecurity professionals have been predicting an impending malware onslaught originating from Internet of Things (IoT) devices—“smart” everyday household items that can connect to the Internet, such as refrigerators, WiFi routers, DVRs, baby monitors, security cameras, thermostats, and so forth.
During 2016, the future became the ‘here and now’ as cyber-criminals recruited well over 1,000,000 IoT devices to expand their zombie armies.
Two primary source code families—Mirai and Bashlight—were the weapons of choice. Both source codes exploit weaknesses in the device’s telnet remote connection protocol on devices running a Linux protocol called BusyBox. In the case of Mirai, the botnet software also encrypts the data passing between the devices and the command and control (C&C) servers, making it difficult for cybersecurity professionals to monitor and block malicious activity. Researchers also believe that Mirai has taken control of devices previously infected with Bashlight, and possibly even patched them, so the device cannot be infected by a rival botnet.
Krebs Unmasks Mirai
The extent of the Mirai botnet’s power came to light last September, when cybercriminals targeted security researcher Brian Krebs’ website — www.krebsonsecurity.com — with a DDoS attack. Krebs reported that the attack generated an estimated 665 Gigabits of traffic per second at its peak, one of the largest single Internet attacks ever recorded.
This led to the longest story ever published on krebsonsecurity.com this past January, in which Krebs’ describes the lengthy process of discovering the person using the pseudonym “Anna Senpai,” who claimed to be the author of Mirai.
Krebs traces the background to the attack on his site from his own investigation into revealing that “vDOS” — one of the largest and longest-running DDoS-for-hire services — had been hacked, exposing details about the services owners and customers. Hours after the story ran, the two 18-year-old Israeli men described in the story as the owners of vDOS were arrested by Israeli authorities, and vDOS was shut down.
As told by “Anna Senpai” himself in a series of chat messages, the Mirai botnet was rented out to someone upset by the arrests, who then revenge-targeted KrebsOnSecurity with the 620 Gbps attack. According to the chat messages, Anna Senpai was not aware of the target prior to the attack and seems to regret it, referring to Brian Krebs as “a cool guy”.
In the article, Krebs traces the complex connections between Minecraft servers, DDoS mitigation services, hacker forums, anime fans, and programming languages, and combines these with several sources and corroborating evidence to identify Anna Senpai as Paras Jha, a Rutgers University student and owner of DDoS protection provider Protraf Solutions.
Krebs also describes how Mirai botnet’s control server was taken offline — an action that disconnected many of the bots infected with Mirai from control servers, drastically reducing the botnet’s DDoS power.
IoT Botnet Growth Factors
Even though Mirai remains damaged, it’s not the time for complacency. IoT botnets are particularly dangerous for several reasons, as discussed in Cyren’s recently released special report on botnets. First, there is essentially an unlimited supply of Internet-connected devices — today almost everything is a “smart” device. Second, these Internet-connected devices are usually poorly protected, often lacking basic security programming. Third, Anna-senpai released the code for free in October, providing every hacker on the street the opportunity to build their own botnet. And for those into specialization of labor, researchers report that IoT botnets ranging in size from 100,000 to 400,000 devices can be hired for $3,000 to $7,500 per attack, making their creation and use all the more attractive to criminals.
Want to learn more about cloud-based email & web security? Contact us here!