According to Microsoft, Safe Links is a feature of Microsoft 365 Defender (f.k.a. Advanced Threat Protection, Microsoft Defender for Office 365) that helps protect from users clicking on malicious URLs in emails. This feature provides URL scanning as well as rewriting of inbound emails within the mail flow, and time-of-click URL and link verification. Safe Links scans on top of regular anti-spam and anti-malware solutions and works to protect your organization from malicious phishing links.
How Do Safe Links Work?
Safe Links begin by analyzing non-whitelisted links from known malicious sites. If URLs are identified as potentially suspicious, you may be blocked from opening that URL when you click on it. Instead of going to the site, you will see a warning page first.
It’s much easier to explain Safe Links and URL rewriting with examples and diagrams. Let’s use three URLs from an imaginary email message:
- A safe website – www.amazon.com
- Let’s pretend this is a well-known phishing site –www.Phishing-R-Us.com
- We’ll use this as a new, uncategorized website – www.o365-shop.com
Safe Links rewrites the above URLs a format similar to these:
- na01.safelinks.protection.com/?url=www.amazon.com
- na01.safelinks.protection.com/?url=www.phishing-r-us.com
- na01.safelinks.protection.com/?url=www.o365-shop.com
Due to the magic of HTML, Microsoft ATP can rewrite URLs without changing how they’re displayed to the users. For the most part, users only know if ATP has written a URL if they click and watch the location bar in their browsers.
![]()
Figure 1 A Safe Links URL in the browser location bar
When a user clicks one of these rewritten URLs, they are first directed to the na01.safelinks.protection.com server which checks if the destination URL, defined in the portion of the URL after the equal sign, is safe or a threat. If the URL is safe, the user is redirected to the destination as though nothing ever happened – although there is often a noticeable delay. If the URL is a threat, the user is redirected to a warning page instead of the intended destination.
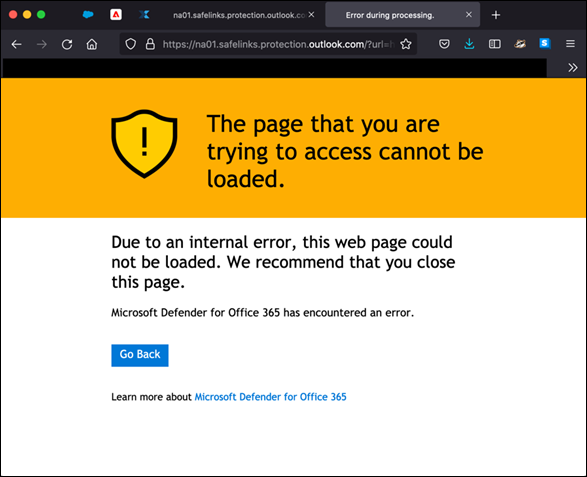
Figure 2 Safe Links blocking access to a phishing page
The intent of URL rewriting is to provide something called time of click protection. It’s a belt and suspenders approach to applying static threat databases to defend against phishing. If the URL isn’t known to be a threat at the time it’s scanned (prior to delivery) then URL rewriting allows the email security server to check again when a user clicks the URL. However, there are a few problems with this approach:
- URL rewriting cannot be applied to URLs in files attached to a message or files shared from, for example, Google Drive. Attackers know this and Cyren has observed a big increase in the number of phishing URLs contained in files.
- Since the display name of the URL isn’t rewritten, users can simply copy that text and paste it into a browser. I do this all the time to skip the delay associated with the email security server.
- Security is only as effective as your threat intelligence. We’ve found the best way to identify zero-day and targeted phishing URLs is to analyze them in real-time.
- URL rewriting can break the association of URLs and apps on your phone. I just ran into this when trying to reset the password for a mobile app using a reset link delivered to my inbox.
- URL rewriting is reactive, so administrators still need to respond to threats. Really what you need is a system that not only continuously detects phishing threats as they evolve but can also automatically remediate all the affected messages.
Frequently Asked Questions About Office 365 Safe Links
What Part of 365 Does Safe Links Impact?
Safe Links specifically look and try to protect you from email phishing links/web sites which are known to contain malicious software and links in SharePoint and OneDrive.
What Do I Do When I Encounter a Safe Links Protection Page?
You’ll want to verify that the website you were attempting to access is using the correct URL. Oftentimes misspelled words or certain sets of characters in the site name will try to trick you into thinking it is a reputable site.
Where are Safe Links Available?
Here are some of the places that Safe Links can be enabled:
- Email: Microsoft’s built-in protection policy provides Safe Links protection to all recipients. That said, you can also create specific Safe Links policies which apply to specific users, groups, or domains.
- Microsoft Teams: Safe Links can protect you from potentially malicious links in Teams conversations, group chats, or even from channels also controlled by Safe Links policies.
- Office 365 Apps: Office 365 Safe Links protection is available in desktop, mobile, and also web app formats.
Final Thoughts
Safe Links is a handy feature to secure Microsoft Office 365. Just don’t let it give you a false sense of security. No single feature or solution can address all email security threats. We’ve found the best approach is to leverage everything Microsoft Defender for Office 365 (read: ATP) provides and complement it with a specialized anti-phishing and automated incident response solution. This combination allows you to filter out the known threats and then continuously scan and remove targeted and zero-day phishing.
Learn more about Cyren Inbox Security, which helps to continuously scan for and automatically remediate email threats in Microsoft 365 mailboxes.
