Wix allows anyone to create a free website with simple point, click and drag formatting. Of course, “anyone” can include phishers and malware distributors, and we at the Cyren Security Lab discovered earlier this week just such abuse of a Wix page targeted at Office 365 users, the subject of this article in InfoWorld. Once we notified Wix, they immediately removed the page, but it’s a critical reminder that a “no trust” philosophy is paramount when it comes to web security, even (and especially) when accessing a brand you trust, like Wix.
The advantages for the phisher of using Wix are:
- Free hosting of the phishing page
- Because the domain is very popular, it isn’t blocked by many URL filtering and web security products
The phishing site, which targeted Office 365 users, was very simple and did not use phishing-related terms — we believe based on the assumption that Wix would scan for these and take down the site.
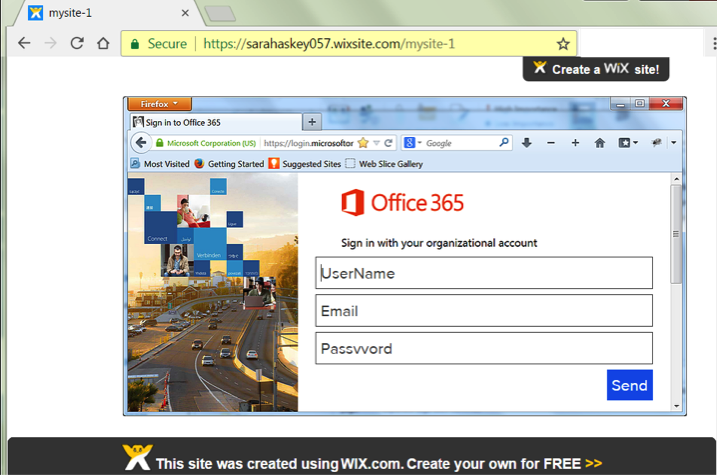
As shown above, the phishing site consisted of a screenshot of an Office 365 login page with login fields overlaid on the screenshot. There is, therefore, no text on the page relating to Microsoft or Office 365 – it’s all image-based. Also the password field is actually spelled with two “v”s, as in “passvvord”. The separation of the image and the fillable phishing fields is clearly shown when accessed on a mobile device:

Cyren Web Security and URL filtering users are protected from this and similar threats. Evidently web platform services providers need to be vigilant and constantly review opportunities to enhance security for their customers and those customers’ users.