The Covid-19 pandemic not only killed millions of people, but it also drastically changed the retail landscape. In fact, you could say that it killed the retail industry.
However, this fact was not a disadvantage for phishers; loads of shops started functioning online, leaving a great opportunity for the bad guys to start their activities.
According to the APWG Phishing Activity Trends Report, e-commerce/retail is the fifth most targeted industry in 4Q 2020 (8.9 % of phishing). It does not sound much, but the loss of hard-earned money combined with the global pandemic is hard to cope with.
The Attack
With Cyren Inbox Security (CIS) you can prevent a lot of life’s disappointments because, as we all know, CIS is First to Detect, First to Protect, and we can also say First to Save your Money.
Let’s take a look at an example of a marketplace phishing. If you have already lost money due to phishing and you have not yet purchased CIS then you can protect yourself from another attack by reading this article.
Ebay, the most popular marketplace all over the world, appears to be a big lake for attackers to hook users’ credentials.
For these attacks, cybercriminals try to mislead their victims into thinking that a seller asked eBay customer service to look into the case and make a final decision.
In the email header the word eBay is used, and an inexperienced person would believe that the email was sent from them. If we look closely, we will see that domain in the sender’s address is not ebay.com. The sender’s display name is eBay, but the address is ebay@ileesho.com or ebay@souvenirgroups.com.
This is a weird decision for eBay customer support to send automatically generated emails from such addresses. With the service whois, it is very easy to look up the owner of these untrustworthy domains. The owner of the ileesho.com is “WhoisSecure,” and souvenirgroups.com belongs to “THE ENDURANCE INTERNATIONAL GROUP, INC.” These organizations are clearly not eBay. “WhoisSecure” means that the owner of the domain is hiding their identity. The domains were recently created as well as registered only for one year. This constitutes inappropriate behavior for a company created back in 1995. This should be a warning to not fully trust the email, but not many users will do this level of investigation before clicking a link.
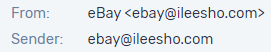
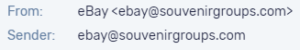
Phishing email headers
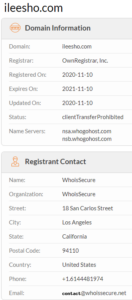
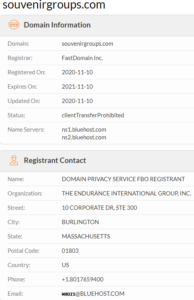
Checking domain owners with the whois service
In the email body the phrase, “The seller asked us to look into this case and make a final decision,” can cause panic by thinking that something is wrong with the order and urge the victim to click on the “View Case” button.
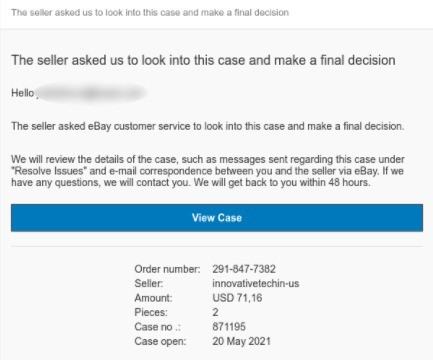
Phishing email body
After clicking on the malicious button, a nervous buyer will see an Ebay login page, where phishers kindly have already inserted the user’s email address. All that is left, is to click the “Continue” button. Or it is better to call it then “Continue to the nightmare of lost credentials” button. Pay attention to the protocol of the page – http – which means “not a secure connection” due to the lack of “s” in the end. This should be the second warning for the recipients.
Phishing attacks have become more extravagant so even if you see https:// in the beginning of the URL, it does not always mean that the site is legitimate. Just because a connection is encrypted does not mean that it is safe to input your credentials. If you want to dive deeply into this topic (and you should!) please read – How Phishers Abuse Hypertext Transfer Protocol Secure (HTTPS) Protocol.
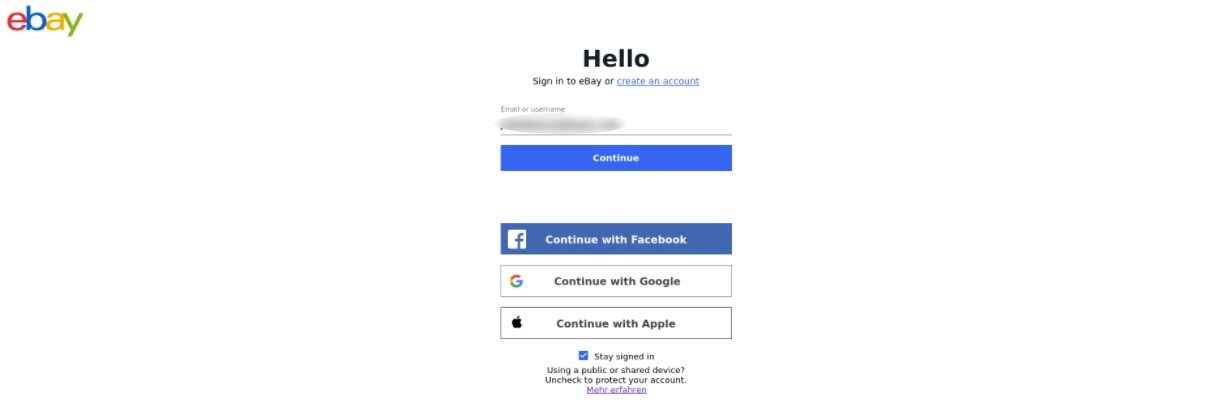
Fake eBay login page
Then the most desired page for phishers will open. A page where the victim should input the precious password. The Beatles sing “All you need is love”, but the Phishers sing “All we need is your password”.
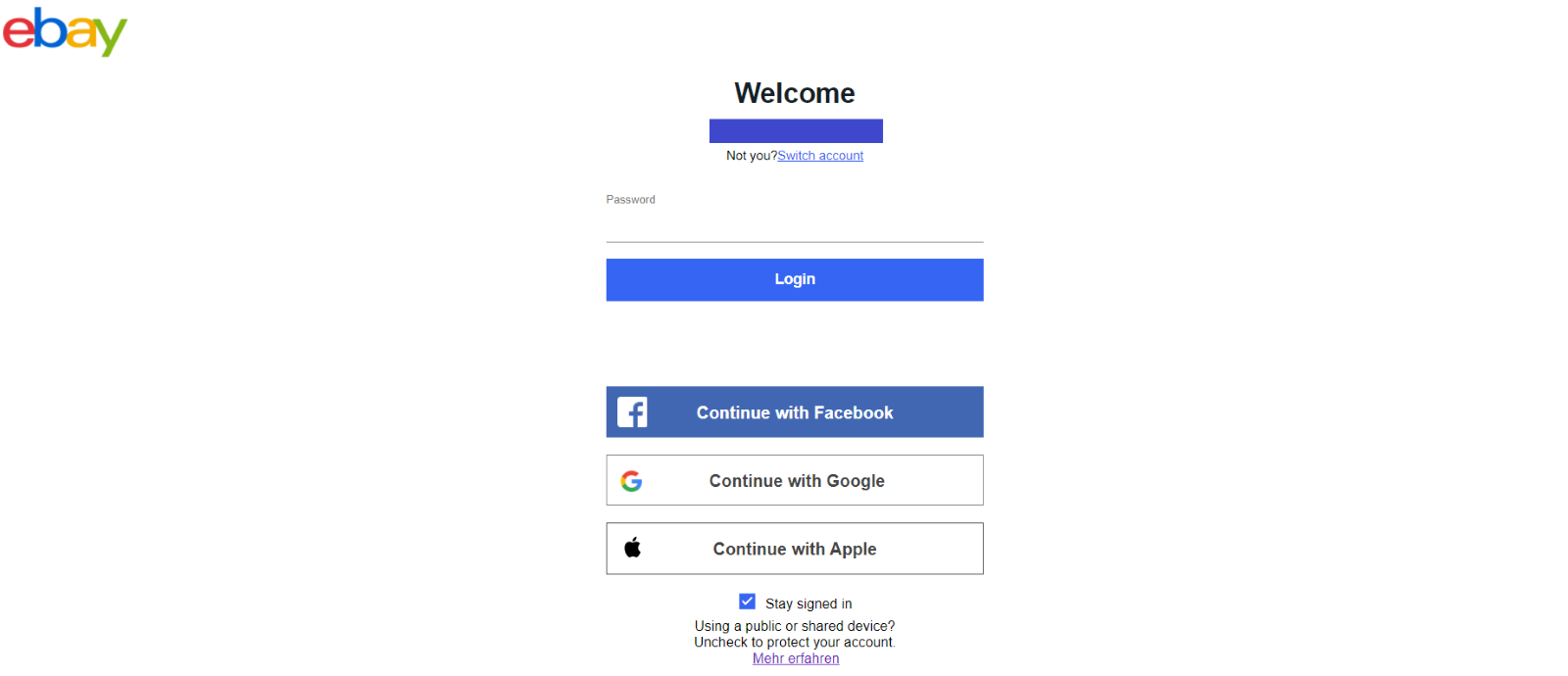
Fake eBay login page
Not being scammed is a good reason to start using Cyren Inbox Security? Decide for yourself and Start a 30-day trial >
